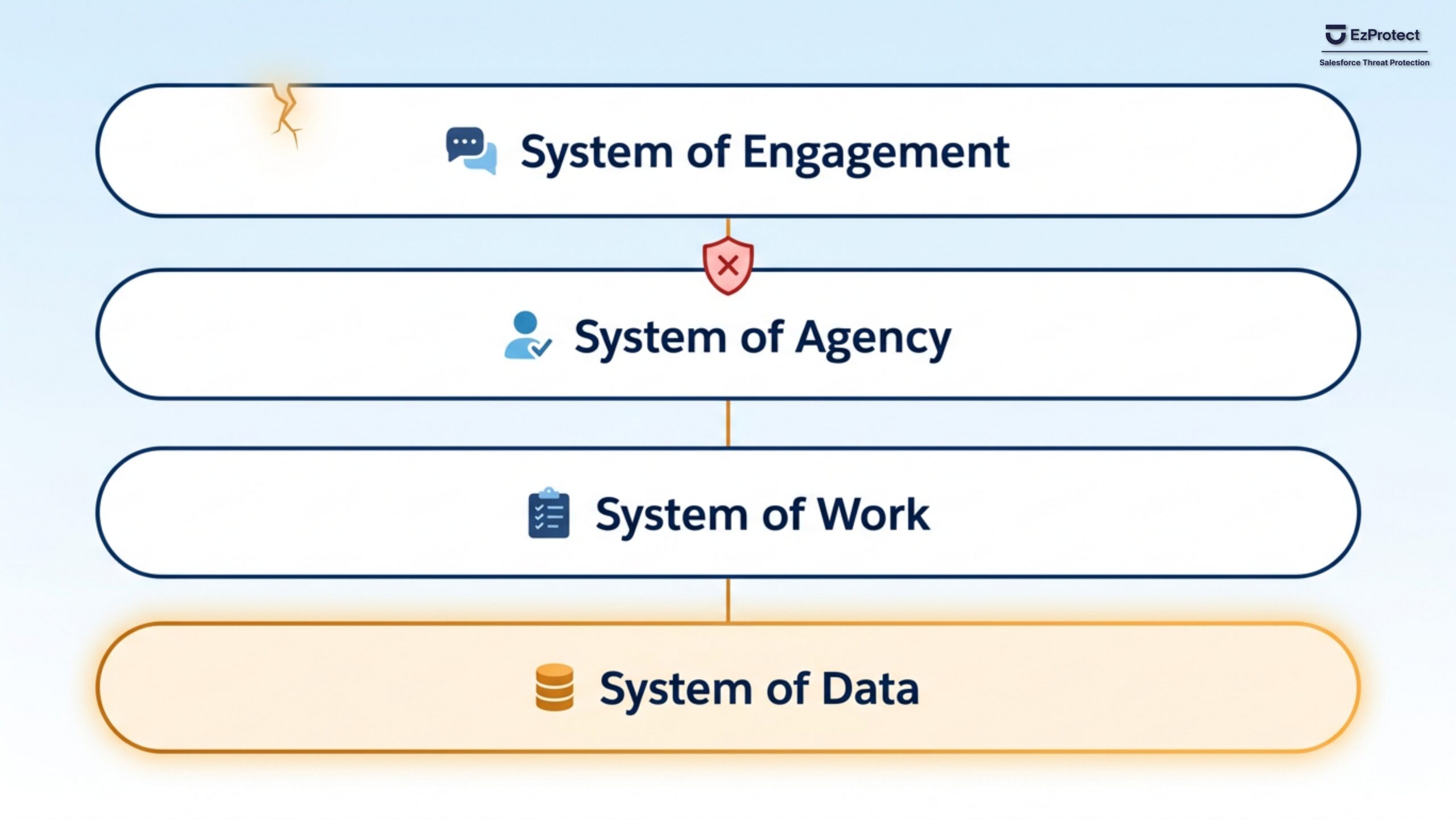
Salesforce Built Four Connected Layers. Attackers Are Already Inside One of Them.
Salesforce's new Agentic Enterprise architecture has four connected layers. Attackers are already inside one. What CISOs need to know.
ClickFix, OAuth Exploits, and AI Phishing: A Salesforce Security Briefing for U.S. Federal Teams
U.S. federal Salesforce teams face AI phishing, OAuth exploits, and nation-state campaigns. Learn where platform security leaves gaps and how to close them.
EzProtect Renews ISO 27001 Certification, Maintaining Annual Third-Party Validation for Salesforce Security
EzProtect renews ISO 27001:2022 certification for 2026, validating world-class security standards for its purpose-built Salesforce threat protection.
Why Stolen OAuth Tokens Are Still Opening Doors to Salesforce Customer Data
Grubhub confirmed attackers accessed Salesforce and Zendesk data using OAuth tokens stolen months earlier. Learn why 700+ organizations were affected and how to protect your Salesforce customer data from the same attack chain.
10 Salesforce Security Tips Architects Need to Know in 2026
Learn 10 critical Salesforce security practices for architects covering OAuth token management, External Client Apps migration, AI governance, and breach recovery planning
Salesforce Hit with 70+ Lawsuits, But Who’s Really at Fault?
Salesforce faces 70+ lawsuits after data breaches. Learn why these attacks were preventable and what you must do now.
How Ransomware Enters Salesforce Environments Through Unscanned Files
Gain a deeper understanding of how ransomware enters Salesforce environments through unscanned files.
The Salesforce Security Checklist Guide for Salesforce Admins: 10 Critical Steps to Prevent and Contain Data Breaches
Prevent and contain data breaches in your Salesforce instances with this essential 10-step security checklist for admins.
Are Your AppExchange Packages Putting Your Salesforce Data at Risk?
Uncover why AppExchange packages create hidden Salesforce security vulnerabilities and the specific questions security teams must ask to prevent data breaches.