How Salesforce Admins Should Audit Connected Apps Before Migrating to External Client Apps
Marija Petronijevic and Matt Meyers,CTA walk Salesforce admins through auditing and migrating Connected Apps to External Client Apps using the TIME framework.
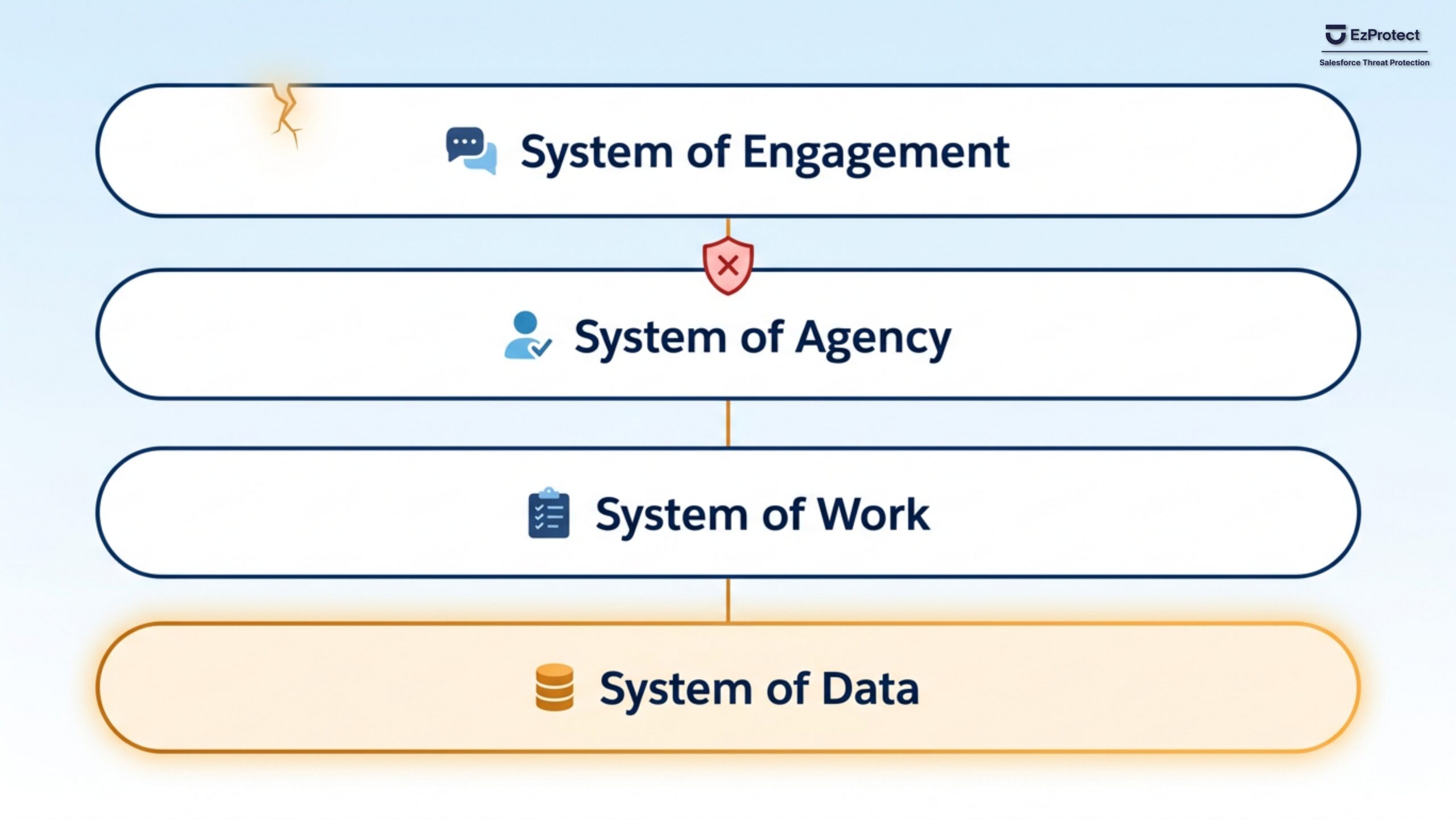
Salesforce Built Four Connected Layers. Attackers Are Already Inside One of Them.
Salesforce's new Agentic Enterprise architecture has four connected layers. Attackers are already inside one. What CISOs need to know.
Secure Custom Portal Architecture for Architects: Building on Salesforce as Your Data Source
Jessie Grenfell breaks down secure Salesforce portal architecture: JWT auth, row-level security in Apex, record ID obfuscation, and MuleSoft vs. AWS.
Salesforce Configuration Drift: A DevSecOps Security Guide
Richard Clark and Matt Meyers break down Salesforce configuration drift, DevSecOps, and change tracking to stop breaches before they start.
What Every Salesforce Team Needs to Know About Security and Agentforce Vibes
Learn how to vibe code securely in Salesforce. Beech Horn covers MCP risks, supply chain attacks, and safe Agentforce Vibes development.
ClickFix, OAuth Exploits, and AI Phishing: A Salesforce Security Briefing for U.S. Federal Teams
U.S. federal Salesforce teams face AI phishing, OAuth exploits, and nation-state campaigns. Learn where platform security leaves gaps and how to close them.
EzProtect Renews ISO 27001 Certification, Maintaining Annual Third-Party Validation for Salesforce Security
EzProtect renews ISO 27001:2022 certification for 2026, validating world-class security standards for its purpose-built Salesforce threat protection.
Why Stolen OAuth Tokens Are Still Opening Doors to Salesforce Customer Data
Grubhub confirmed attackers accessed Salesforce and Zendesk data using OAuth tokens stolen months earlier. Learn why 700+ organizations were affected and how to protect your Salesforce customer data from the same attack chain.
What to Do in the First 24 Hours After a Salesforce Data Breach
Learn the critical steps to take in the first 24 hours after a Salesforce data breach using the NIST Threat Response Lifecycle.